We are Foxway
We enable circular tech

What we do
Our circular services
We help large organizations, the public sector and resellers of consumer electronics to become more circular in the way they think and act. To be specific, we provide our partners and customers with different services that help them to manage mobile phones, computers and other tech devices in a way that is both cost-efficient and sustainable.
We call it Circular Tech.
Recovery Services
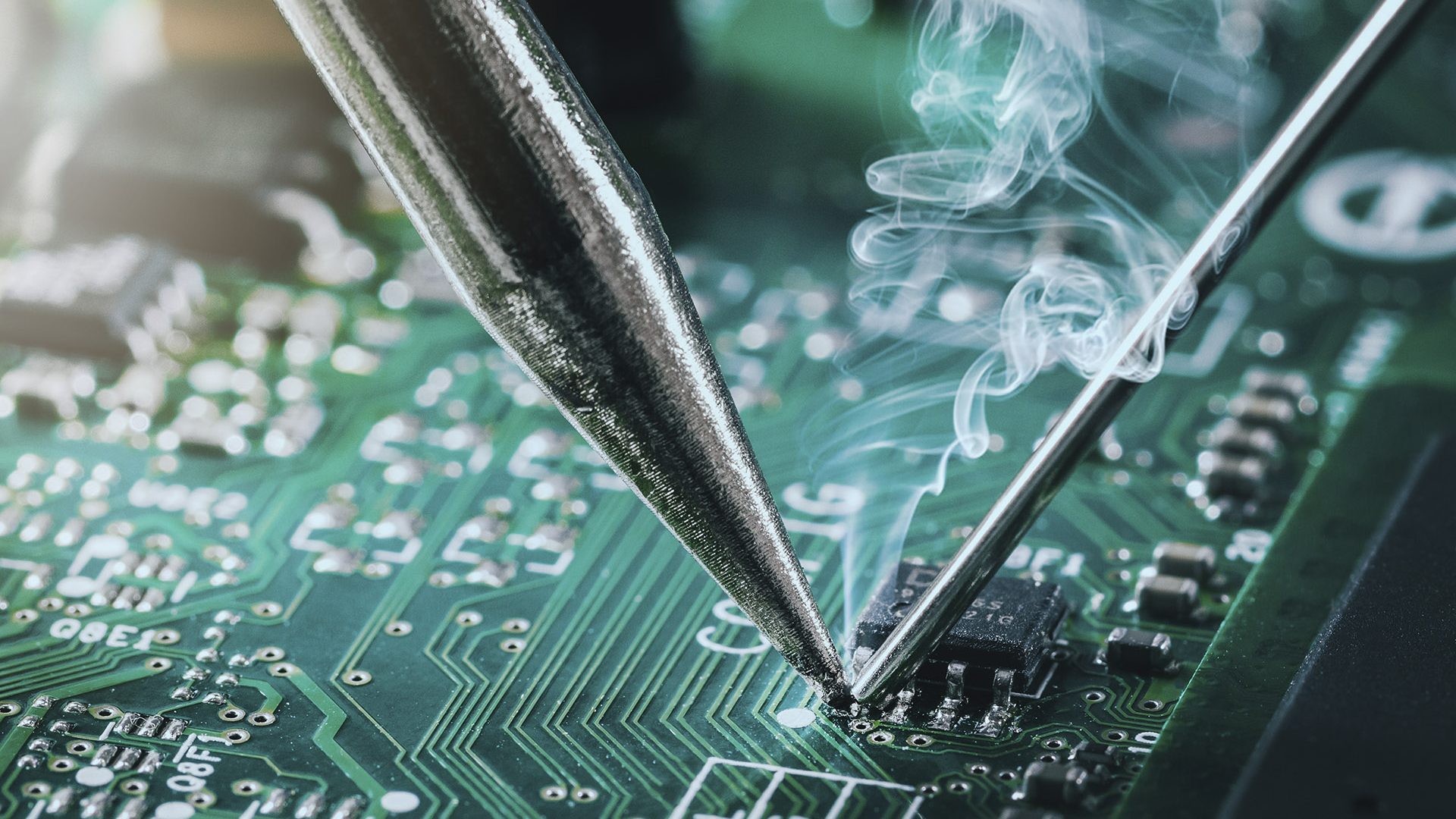
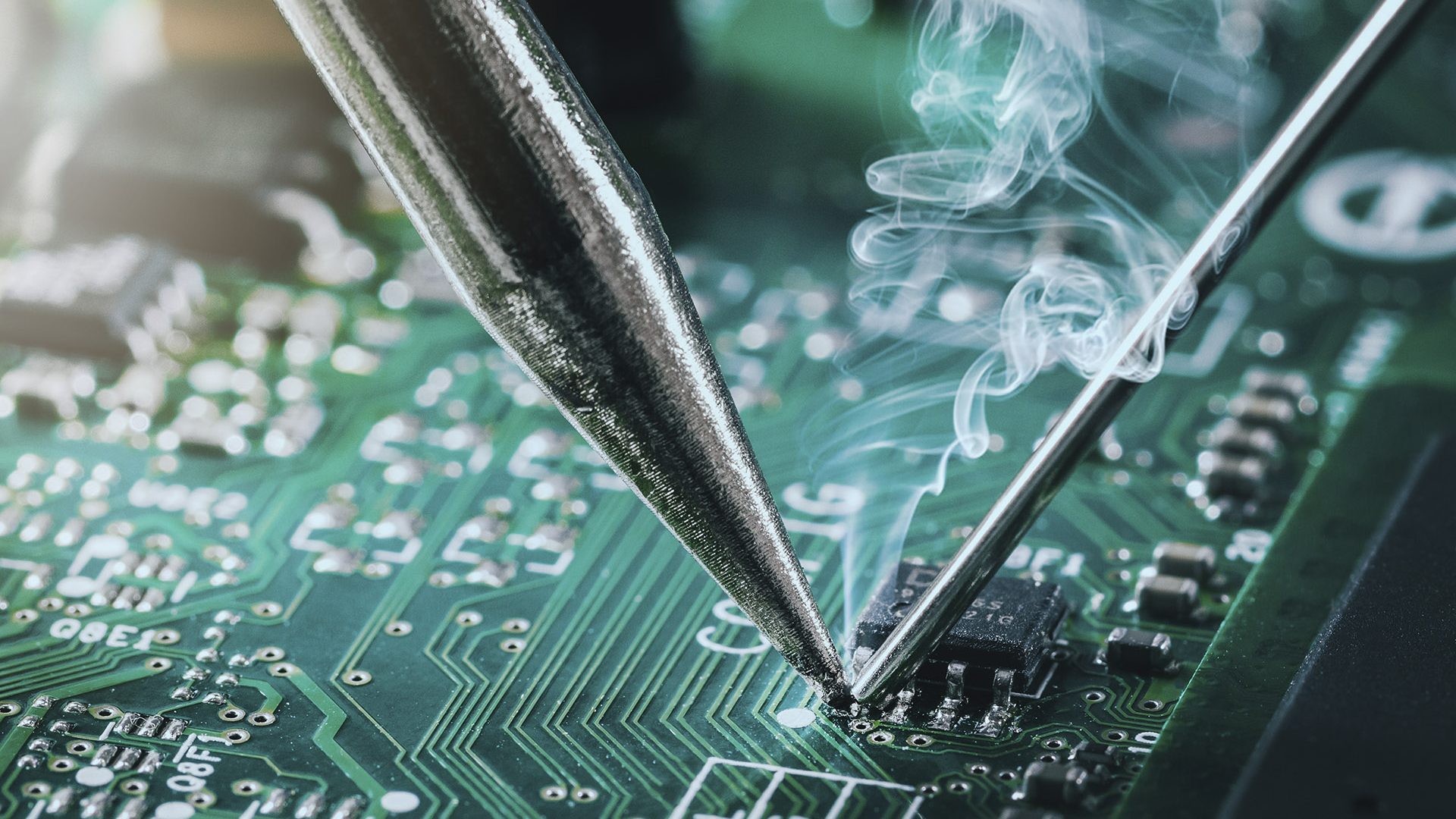
We offer a range of services to take back used devices, such as computers and mobile phones, so the current users get a smooth transition when it is time to upgrade. When the products come back to us, we ensure the safe deletion of data before we repair and refurbish them. We also offer buyout solutions for overstock.
IT Asset Disposition (ITAD)
Residual value return by giving a new life to the tech devices you no longer use.

Future Price Commitment
Service guarantees the future trade-in price of products at time of initial sale.

Asset Management
Manage your end-of-life, end-of-lease, and overstock tech devices and parts.

Retail Trade-In Solution
Get a new device for a fraction of its price from trade-in value.

B2B - Buyback Solution
We support channel partners to enable returns from your business customers.

OEM Buyback Solution
A hassle-free solution to help you accelerate tech refresh.
Remarketing Services

Redeployment Services
Return your devices to us for refurbishment to reuse in your organization.
Fast Swap Solution
Forward & return process by supplying the customer with a new device.

Hassle-Free Replacement
Smooth swap process of devices, easily managed by our platform.
Repackaging Services
Tailored repackaging for refurbished tech products.

OEM Returns Management
We will buy the irregular or devices that haven’t been sold.

Localization Services
We purchase your overstock and relocate it to a new region.
Advisory & Insights

Tech Solution – Advisory
We support you in making strategic refresh tech decisions.
Self-Service Portal
Reporting the environmental footprint of your organization’s tech devices.

Data Centre Infrastructure
Securely manage return of hardware, selling into secondary markets.

Sustainability Reporting
Understand the sustainability impact of your organization’s tech.

Process Advisory
Strategies for the private, public and social sector organizations.

Customized Handprint Reports
Calculate the beneficial greenhouse gas impacts of a product.